IPEERION IP STRATEGY – THE FUTURE OF B2B COMMERCE
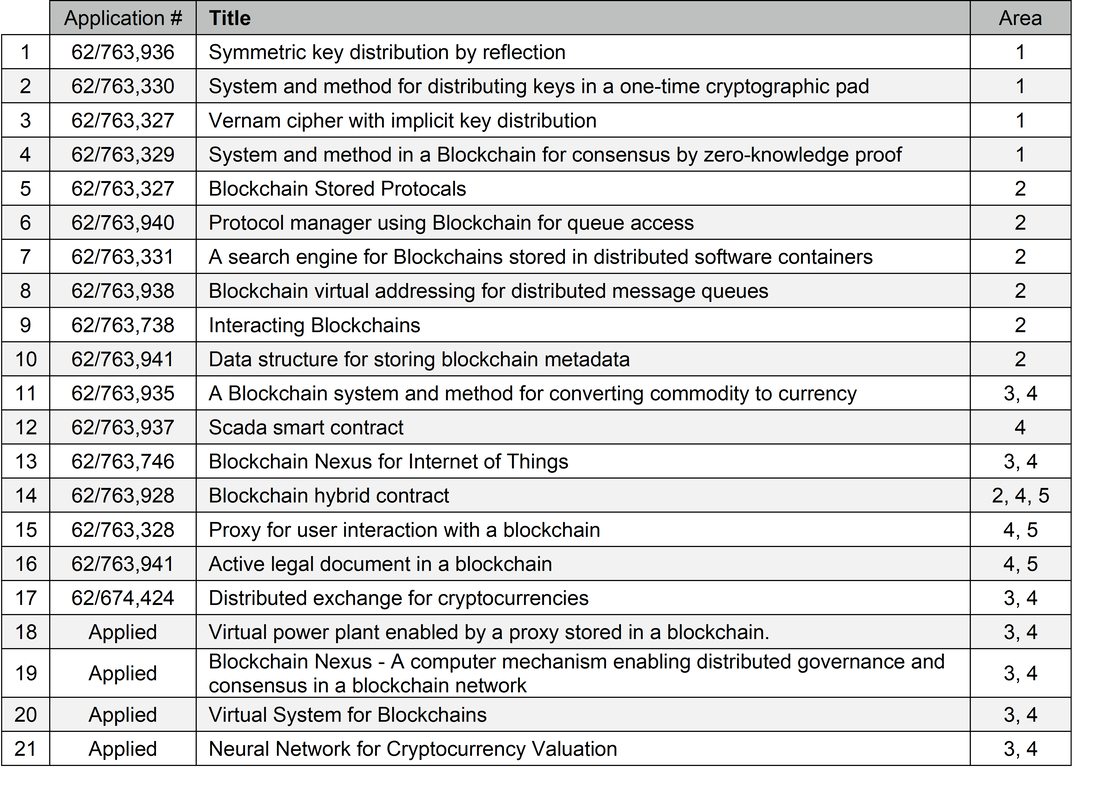
iPeerion designed, wrote and filed patents to denote and protect iPeerion breakthroughs in blockchain technology crucial to the future of B2B commerce. In the process of filing these 19 interlinked patents, iPeerion has also completed a cursory review of existing patents in the corresponding blockchain arena and found the majority to be, in general, repetitive (cryptocurrency centric), lacking substance and poorly written. iPeerion’s patents, designed and written by David Orr, are well-founded, substantial, defensible, and pertinent to where B2B blockchain must go. David Orr, PhD, iPeerion’s Chief Scientist, has written in excess of 200 patents and has been a patent defense consultant to major companies, including Microsoft, Intel and Micron.
iPeerion designed, wrote and filed patents to denote and protect iPeerion breakthroughs in blockchain technology crucial to the future of B2B commerce. In the process of filing these 19 interlinked patents, iPeerion has also completed a cursory review of existing patents in the corresponding blockchain arena and found the majority to be, in general, repetitive (cryptocurrency centric), lacking substance and poorly written. iPeerion’s patents, designed and written by David Orr, are well-founded, substantial, defensible, and pertinent to where B2B blockchain must go. David Orr, PhD, iPeerion’s Chief Scientist, has written in excess of 200 patents and has been a patent defense consultant to major companies, including Microsoft, Intel and Micron.
|
PATENT STRATEGY BASED ON DECADES OF EXPERIENCE
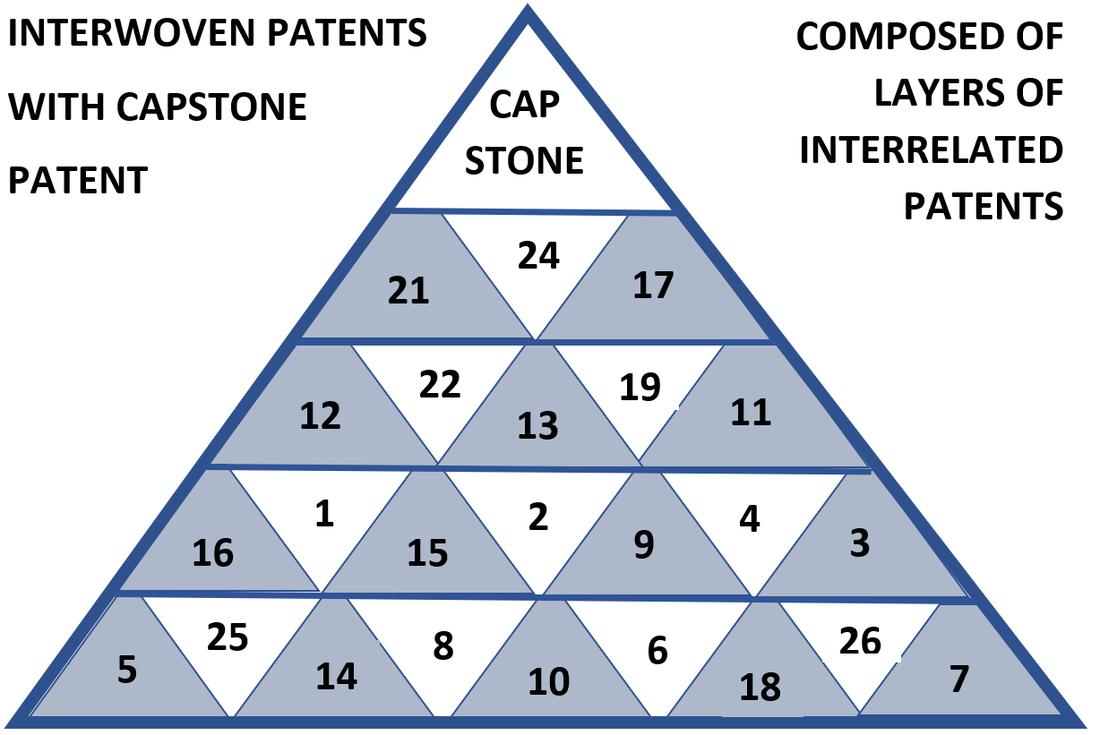
iPeerion has carefully constructed their family of Patents to be interlocking as shown below. In this fashion the body of work is built underneath and to support a capstone patent, creating cohesion and greater protection, if and when patent defense is needed. Each patent provides the minimum information required to define it and the contained claims. The Capstone patent is the most general but strongly supported by the patents (and associated technology) built to enable it (in essence its building blocks). In this document, number 20 (VIRTUAL SYSTEM FOR BLOCKCHAINS) is the Capstone patent. |
IPEERION CORE COMPONENTS
|
A. Encryption: Specifically, quantum computer resistant iCipher by iPeerion. As quantum computers become an everyday part of the tech landscape, traditional forms of encryption, that would take today’s supercomputers hundreds of years to break may become vulnerable when crunched by a quantum computer. Many experts believe that these security disruptions are already on the horizon and there is a growing need for alternate forms of encryption that can maintain security in future blockchain and beyond. iPeerion iCipher based encryption is covered by four (4) patents (see below) and employees strategies including distribution of key by Boolean functions, symmetric key cryptography, Vernam cipher (mathematically proven to be unbreakable even buy a quantum computer) with key distribution by reflection (using a pseudo-random source for key generation - two to the power of 500 keys without repetition) and consensus by zero knowledge proof.
B. Intelligent Protocols: The iPeerion Protocol is a generalization of the “smart contract” concept and includes smart contracts, project management, cooperative planning, peer collaboration and work-flow, loose agreements, and are capable of real-time telemetry data collection and control processes. The iPeerion protocol works across wide geographical areas in widely diverse work settings. iPeerion protocols are stored as “libraries” in a blockchain, and implement distributed governance and consensus according to contract, plan or agreement. C. Nexus: The iPeerion Nexus combines two software systems that interact with Intelligent Protocols – an iPeerion Blockchain Search Engine and Message-Queue Management System. The iPeerion Search Engine:
ii. Application to Database; iii. Application to IoT (Internet of Things) Device; and iv. IoT device to IoT device. The iPeerion Message Queue Manager, under control of the Intelligent Protocol sequences, schedules and controls peer interactions by controlling the messaging network. Through Nexus control of distributed message queues iPeerion will be capable of more than 140,000 blockchain updates per second. |
D. Transaction Speed: A key factor in block chain today (and critical in the future is distributed transaction speed). iPeerion can process in excess of 140,000 secure transactions per second which is 10 times major credit card companies maximum throughput and hundreds of times processing rates of existing blockchain strategies. This is accomplished using iPeerion iCipher, which is the only encryption today that is quantum computer proof, deploying versatile iPeerion “super-smart” contracts (iProtocol) that allow real-time intelligent complex transactions (safe, secure, programmed, immutable and fast) across department, business, industry and international boundaries. Currently covered by six (6) distinct but connected patents see below.
E. Future IP Efforts: We will continue to file patents that give us “dense” coverage in the B2B focus areas. Soon we will begin filing patents based upon B2B e-Commerce blockchain applications. With our current filings, 21 patents, we expect to reach thirty to forty patent applications by early 2019. |
FUNCTIONAL DESCRIPTIONS AND ABSTRACTS
1. SYMMETRIC KEY DISTRIBUTION BY REFLECTION
FUNCTIONAL DESCRIPTION
Part 1 of the method for creating, exchange and use/storage of quantum computer resistant encrypted messages between nodes.
Covers the use of Boolean Functions to encode/enable symmetric key cryptography (Vernam cipher) and key distribution by reflection. By selecting more than one device to send messages, the computer network implements consensus by zero-knowledge proof.
FUNCTIONAL DESCRIPTION
Part 1 of the method for creating, exchange and use/storage of quantum computer resistant encrypted messages between nodes.
Covers the use of Boolean Functions to encode/enable symmetric key cryptography (Vernam cipher) and key distribution by reflection. By selecting more than one device to send messages, the computer network implements consensus by zero-knowledge proof.
ABSTRACT
In a computer network having message senders and receivers, a system and method for creating and storing a data structure in a sending device and sending data to a receiver. The data structure, forming the domain of a Boolean function, comprises the sending device digital signature, a biometric signature of the sending device operator, the previous block of the sending device data structure and a data record sent by the receiver. The device computes the Boolean function of said data stored in the sending device and uses the function co-domain to encode the message sent to the receiver. The method described enables symmetric key cryptography- the Vernam cipher- with key distribution by reflection. By selecting more than one device to send messages, the computer network implements consensus by zero-knowledge proof.
In a computer network having message senders and receivers, a system and method for creating and storing a data structure in a sending device and sending data to a receiver. The data structure, forming the domain of a Boolean function, comprises the sending device digital signature, a biometric signature of the sending device operator, the previous block of the sending device data structure and a data record sent by the receiver. The device computes the Boolean function of said data stored in the sending device and uses the function co-domain to encode the message sent to the receiver. The method described enables symmetric key cryptography- the Vernam cipher- with key distribution by reflection. By selecting more than one device to send messages, the computer network implements consensus by zero-knowledge proof.
2. SYSTEM AND METHOD FOR DISTRIBUTING KEYS IN A ONE-TIME CRYPTOGRAPHIC PAD
FUNCTIONAL DESCRIPTION
Part 2 of the method for creating, exchange and use/storage of quantum computer resistant encrypted messages between nodes.
Covers sending messages between cryptographic peers programmed to generate identical pseudo-random bitstreams of an arbitrary number of bits (one-time pad). Includes coordination of message length (number of bits), duplication, extraction, hashing, verification and decryption.
FUNCTIONAL DESCRIPTION
Part 2 of the method for creating, exchange and use/storage of quantum computer resistant encrypted messages between nodes.
Covers sending messages between cryptographic peers programmed to generate identical pseudo-random bitstreams of an arbitrary number of bits (one-time pad). Includes coordination of message length (number of bits), duplication, extraction, hashing, verification and decryption.
ABSTRACT
In a peer-peer computer network, a system and method for generating and distributing a one-time pad among multiple cryptographic users, and interchanging messages encrypted by the one-time pad. A network of cryptographic peers; said cryptographic peers programmed to generate identical pseudo-random bitstreams, PR, of an arbitrary number of bits is disclosed. In the network, peer A (PA) wishes to send a message, M, to peer B (PB). PA sends a n-tuple (NT) of integers, TI- NT(TI) to PB. NT(TI) may be encrypted. PB decodes NT(TI)- if necessary- and extracts one integer from TI and, using it as an index, extracts pre-determined number-K bits from pseudo-random source PR. PB hashes the K bits and sends the hashed K bits- HKB- back to PA. PA, having duplicated PB’s bit extraction and hashing for all indices in NT(TI), compares the hash sent by PB. Having determined the index selected by PB, PA extracts N bits from PR, and forms a symmetric key SK. PA encrypts M using the SK formed from the selected bits of PR. PA selects ML bits, where ML is the message length. PA sends the encrypted message M- E(M)- to PB, where PB decrypts with the same symmetric key used by PA. The one-time pad may be advanced by both PA and PB jointly inserting a portion of the encrypted message into PR.
In a peer-peer computer network, a system and method for generating and distributing a one-time pad among multiple cryptographic users, and interchanging messages encrypted by the one-time pad. A network of cryptographic peers; said cryptographic peers programmed to generate identical pseudo-random bitstreams, PR, of an arbitrary number of bits is disclosed. In the network, peer A (PA) wishes to send a message, M, to peer B (PB). PA sends a n-tuple (NT) of integers, TI- NT(TI) to PB. NT(TI) may be encrypted. PB decodes NT(TI)- if necessary- and extracts one integer from TI and, using it as an index, extracts pre-determined number-K bits from pseudo-random source PR. PB hashes the K bits and sends the hashed K bits- HKB- back to PA. PA, having duplicated PB’s bit extraction and hashing for all indices in NT(TI), compares the hash sent by PB. Having determined the index selected by PB, PA extracts N bits from PR, and forms a symmetric key SK. PA encrypts M using the SK formed from the selected bits of PR. PA selects ML bits, where ML is the message length. PA sends the encrypted message M- E(M)- to PB, where PB decrypts with the same symmetric key used by PA. The one-time pad may be advanced by both PA and PB jointly inserting a portion of the encrypted message into PR.
3. VERNAM CIPHER WITH IMPLICIT KEY DISTRIBUTION
FUNCTIONAL DESCRIPTION
Part 3 of the method for creating, exchange and use/storage of quantum computer resistant encrypted messages between nodes.
Covers generating and distributing a one-time pad among peers, and exchanging messages encrypted by the one-time pad. The peers generate/identify a (next) common extremely long pseudo random sequence from an accessible source, and using a previously known index, identical streams are selected and are used as a symmetric key in the (next) encrypted message exchanged. Pseudo random means 2 to the power of 500 sequences can be used without repetition.
FUNCTIONAL DESCRIPTION
Part 3 of the method for creating, exchange and use/storage of quantum computer resistant encrypted messages between nodes.
Covers generating and distributing a one-time pad among peers, and exchanging messages encrypted by the one-time pad. The peers generate/identify a (next) common extremely long pseudo random sequence from an accessible source, and using a previously known index, identical streams are selected and are used as a symmetric key in the (next) encrypted message exchanged. Pseudo random means 2 to the power of 500 sequences can be used without repetition.
ABSTRACT
In a peer-peer computer network, a system and method for generating and distributing a one-time pad among peers, and interchanging messages encrypted by the one-time pad. A common, extremely long pseudo random sequence is generated by the peers, and by a previously shared secret index, k bit are selected starting at the index offset of the pseudo random sequence. The k-bits are used as a symmetric key in an encrypted message exchanged between peers. M-bits of the exchanged message are selected by the peers and used as a replacement secret offset index for the next encrypted exchange.
In a peer-peer computer network, a system and method for generating and distributing a one-time pad among peers, and interchanging messages encrypted by the one-time pad. A common, extremely long pseudo random sequence is generated by the peers, and by a previously shared secret index, k bit are selected starting at the index offset of the pseudo random sequence. The k-bits are used as a symmetric key in an encrypted message exchanged between peers. M-bits of the exchanged message are selected by the peers and used as a replacement secret offset index for the next encrypted exchange.
4. A SYSTEM AND METHOD IN A BLOCKCHAIN FOR CONSENSUS BY ZERO-KNOWLEDGE PROOF
FUNCTIONAL DESCRIPTION
Part 4 of the method for creating, exchange and storage of quantum computer resistant encrypted messages between nodes.
A trusted “black box” method to establish consensus for blockchain users/peers within a network on the work output of one or more peers, wherein that work is recorded in a blockchain if/when consensus is reached. Method includes secondary (blind) participants (peers) given either permanent or temporary authority to establish consensus (by established protocols) and record (work and associated digital signatures) on the blockchain. This patent covers the paradoxical situation where by two or more parties can arrive at consensus with only partial knowledge of the subject matter.
FUNCTIONAL DESCRIPTION
Part 4 of the method for creating, exchange and storage of quantum computer resistant encrypted messages between nodes.
A trusted “black box” method to establish consensus for blockchain users/peers within a network on the work output of one or more peers, wherein that work is recorded in a blockchain if/when consensus is reached. Method includes secondary (blind) participants (peers) given either permanent or temporary authority to establish consensus (by established protocols) and record (work and associated digital signatures) on the blockchain. This patent covers the paradoxical situation where by two or more parties can arrive at consensus with only partial knowledge of the subject matter.
ABSTRACT
The present invention is a computer method used in a network of blockchain users for reaching consensus on work output, wherein work output comprises a computer record that is recorded in a blockchain if consensus is reached. Work output is made by one or more peers, with possible collaborators, all of whom share in some manner the benefits of the work output. These comprise the first participants, who may disagree on the work output. Second participants are peers, each of whom are given either permanent or temporary authority to authorize recording to a blockchain and benefit from authorizing consensus recording to a blockchain. Each of the first participants is assigned a unique ID. All pairwise exclusive OR products of IDs are formed and sent to the second peer participants. Each of the first participants computes a Merkle tree of that participants version of the work output Each of the first participants encodes their Merkle tree using their ID as a symmetric cryptographic key and broadcasts their encoded Merkle tree to the second participants. Each of the second participants exclusively OR’s, pairwise, each of the encoded Merkle trees to produce a XOR output. If the pairwise first participants agree on work output (identical Merkle trees) the XOR output will be an XOR of the pairwise ID’s of the first participants. Each of the second participants count the number of agreements for each Merkle tree. According to a pre-determined policy, each of the second participants broadcast confirmation of the consensus to peers that record blockchains. Each of the second participants many also send a digital signature of their consensus to peers recording blockchains.
The present invention is a computer method used in a network of blockchain users for reaching consensus on work output, wherein work output comprises a computer record that is recorded in a blockchain if consensus is reached. Work output is made by one or more peers, with possible collaborators, all of whom share in some manner the benefits of the work output. These comprise the first participants, who may disagree on the work output. Second participants are peers, each of whom are given either permanent or temporary authority to authorize recording to a blockchain and benefit from authorizing consensus recording to a blockchain. Each of the first participants is assigned a unique ID. All pairwise exclusive OR products of IDs are formed and sent to the second peer participants. Each of the first participants computes a Merkle tree of that participants version of the work output Each of the first participants encodes their Merkle tree using their ID as a symmetric cryptographic key and broadcasts their encoded Merkle tree to the second participants. Each of the second participants exclusively OR’s, pairwise, each of the encoded Merkle trees to produce a XOR output. If the pairwise first participants agree on work output (identical Merkle trees) the XOR output will be an XOR of the pairwise ID’s of the first participants. Each of the second participants count the number of agreements for each Merkle tree. According to a pre-determined policy, each of the second participants broadcast confirmation of the consensus to peers that record blockchains. Each of the second participants many also send a digital signature of their consensus to peers recording blockchains.
5. BLOCKCHAIN STORED PROTOCOLS
FUNCTIONAL DESCRIPTION
Part 1 of iPeerion mechanism that massively increases speed of transaction through precisely organized distribution across nodes (140,000 plus transactions per second).
Key-Value pairs denoting location, action, location, action (repeat), directing a complex series of blockchain based events towards a predefined outcome (plan). Covers any use of a Blockchain search engine, and encryption (key – value pairs) using data from a variety of sources including web pages. Keys comprise of identifiers, locations and/or descriptors. Values comprise of rule sets, neural nets, code/scripts.
FUNCTIONAL DESCRIPTION
Part 1 of iPeerion mechanism that massively increases speed of transaction through precisely organized distribution across nodes (140,000 plus transactions per second).
Key-Value pairs denoting location, action, location, action (repeat), directing a complex series of blockchain based events towards a predefined outcome (plan). Covers any use of a Blockchain search engine, and encryption (key – value pairs) using data from a variety of sources including web pages. Keys comprise of identifiers, locations and/or descriptors. Values comprise of rule sets, neural nets, code/scripts.
ABSTRACT
A blockchain storing key-value pairs and a search engine for searching the blockchain. Keys comprise:
A blockchain storing key-value pairs and a search engine for searching the blockchain. Keys comprise:
- URI’s or URL’s;
- Device identifiers, or descriptors;
- Application identifiers or descriptors, and;
- Protocol descriptors
- Rule sets for executing a protocol;
- Neural nets as protocols;
- Application code or scripts as protocols;
6. PROTOCOL MANAGER USING BLOCKCHAIN FOR QUEUE ACCESS
FUNCTIONAL DESCRIPTION
Part 2 of iPeerion mechanism that massively increases speed of transaction through precisely organized distribution across nodes (140,000 plus transactions per second).
A system that organizes message queues in blockchain using a content addressing mechanism to map keys to names and values to locations in the network, thus enabling assignment of key – value pairs to producers and consumers of data stored in the queues.
FUNCTIONAL DESCRIPTION
Part 2 of iPeerion mechanism that massively increases speed of transaction through precisely organized distribution across nodes (140,000 plus transactions per second).
A system that organizes message queues in blockchain using a content addressing mechanism to map keys to names and values to locations in the network, thus enabling assignment of key – value pairs to producers and consumers of data stored in the queues.
ABSTRACT
An invention operative in a computer network having a blockchain and message queues. In an exemplary embodiment, the invention creates and assigns key-value pairs to producers and consumers of data stored in the queues. Keys are mapped by the invention to queue labels or names, and values are mapped to queue locations (network addresses.) In the exemplary embodiment the invention also assigns key-value pairs to data records, the key assigned to a record label or name. The invention uses a content addressing mechanism to map keys to locations or network names or network addresses.
An invention operative in a computer network having a blockchain and message queues. In an exemplary embodiment, the invention creates and assigns key-value pairs to producers and consumers of data stored in the queues. Keys are mapped by the invention to queue labels or names, and values are mapped to queue locations (network addresses.) In the exemplary embodiment the invention also assigns key-value pairs to data records, the key assigned to a record label or name. The invention uses a content addressing mechanism to map keys to locations or network names or network addresses.
7. A SEARCH ENGINE FOR BLOCK-CHAINS STORED IN DISTRIBUTED SOFTWARE CONTAINERS
FUNCTIONAL DESCRIPTION
Part 3 of iPeerion mechanism that massively increases speed of transaction through precisely organized distribution across nodes (140,000 plus transactions per second).
Covers development of any search engine for blockchain where that blockchain is distributed over a series of nodes/peers, where the search engine is stored on one of the nodes. Each record searched is stored as a proxy in the distributed network with a bit vector pointer to the storing container.
FUNCTIONAL DESCRIPTION
Part 3 of iPeerion mechanism that massively increases speed of transaction through precisely organized distribution across nodes (140,000 plus transactions per second).
Covers development of any search engine for blockchain where that blockchain is distributed over a series of nodes/peers, where the search engine is stored on one of the nodes. Each record searched is stored as a proxy in the distributed network with a bit vector pointer to the storing container.
ABSTRACT
The present invention is practiced in a network of distributed peers, wherein at least one peer interacts with a software container having a block-chain database.One or more of the peers host a search engine that stores and searches indexes to block-chain records stored in the distributed network. In a first embodiment, each record stored by the search engine comprises a cryptographic hash of part of or all each block-chain record stored within the distributed network. Included with the hash is an address or pointer to the software container storing the block-chain record. In a second embodiment, each record stored and searched by the search engine comprises a proxy to said block-chain record- a bit-vector representing a cryptographic hash of each field of each block-chain record stored in the distributed network. Included with the bit vector is an address or pointer to the software container storing the block-chain record. The bit vector is the co-domain of a surjective mapping of each field in the block-chain record. The co-domain of the mapping can be probabilistically inverted.
The present invention is practiced in a network of distributed peers, wherein at least one peer interacts with a software container having a block-chain database.One or more of the peers host a search engine that stores and searches indexes to block-chain records stored in the distributed network. In a first embodiment, each record stored by the search engine comprises a cryptographic hash of part of or all each block-chain record stored within the distributed network. Included with the hash is an address or pointer to the software container storing the block-chain record. In a second embodiment, each record stored and searched by the search engine comprises a proxy to said block-chain record- a bit-vector representing a cryptographic hash of each field of each block-chain record stored in the distributed network. Included with the bit vector is an address or pointer to the software container storing the block-chain record. The bit vector is the co-domain of a surjective mapping of each field in the block-chain record. The co-domain of the mapping can be probabilistically inverted.
8. BLOCKCHAIN VIRTUAL ADDRESSING FOR DISTRIBUTED MESSAGE QUEUES
FUNCTIONAL DESCRIPTION
Part 4 of iPeerion mechanism that massively increases speed of transaction through precisely organized distribution across nodes (140,000 plus transactions per second).
Covers any use of virtual mapping between messages in a distributed message queue, with mapping and messages stored on the blockchain.
FUNCTIONAL DESCRIPTION
Part 4 of iPeerion mechanism that massively increases speed of transaction through precisely organized distribution across nodes (140,000 plus transactions per second).
Covers any use of virtual mapping between messages in a distributed message queue, with mapping and messages stored on the blockchain.
ABSTRACT
A system and method for virtual mapping to and from messages in a distributed message queue, with a blockchain as a virtual backing store.
A system and method for virtual mapping to and from messages in a distributed message queue, with a blockchain as a virtual backing store.
9. INTERACTING BLOCKCHAINS
FUNCTIONAL DESCRIPTION
Part 5 of iPeerion mechanism that massively increases speed of transaction through precisely organized distribution across nodes (140,000 plus transactions per second).
A system of assigning digital signatures to data structures, digital fingerprints to devices and biometric signatures to device operators on interacting blockchain. Allows the encrypted recording of (sequential, searchable and authenticated) historic activity through use of Boolean functions, symmetric key cryptography, Vernam cipher with key distribution by reflection. Within above records, the involved node network implements consensus by zero-knowledge proof.
FUNCTIONAL DESCRIPTION
Part 5 of iPeerion mechanism that massively increases speed of transaction through precisely organized distribution across nodes (140,000 plus transactions per second).
A system of assigning digital signatures to data structures, digital fingerprints to devices and biometric signatures to device operators on interacting blockchain. Allows the encrypted recording of (sequential, searchable and authenticated) historic activity through use of Boolean functions, symmetric key cryptography, Vernam cipher with key distribution by reflection. Within above records, the involved node network implements consensus by zero-knowledge proof.
ABSTRACT
In a computer network having blockchains, a system and method for creating and storing a first blockchain data structure in a device and sending data to a second blockchain. The data structure, forming the domain of a Boolean function, comprises the device digital signature, a biometric signature of the device operator, the previous block of the device blockchain and a data record sent by the second blockchain. The device computes the Boolean function of said data stored in the device and uses the function co-domain to encode the message sent to the second blockchain. The method described enables symmetric key cryptography- the Vernam cipher- with key distribution by reflection. By selecting more than one device to send messages, the computer network implements consensus by zero-knowledge proof.
In a computer network having blockchains, a system and method for creating and storing a first blockchain data structure in a device and sending data to a second blockchain. The data structure, forming the domain of a Boolean function, comprises the device digital signature, a biometric signature of the device operator, the previous block of the device blockchain and a data record sent by the second blockchain. The device computes the Boolean function of said data stored in the device and uses the function co-domain to encode the message sent to the second blockchain. The method described enables symmetric key cryptography- the Vernam cipher- with key distribution by reflection. By selecting more than one device to send messages, the computer network implements consensus by zero-knowledge proof.
10. DATA STRUCTURE FOR STORING BLOCKCHAIN METADATA
FUNCTIONAL DESCRIPTION
Part 6 of iPeerion mechanism that massively increases speed of transaction through precisely organized distribution across nodes (140,000 plus transactions per second).
Covers a variety of linked blockchain based data structures to store key information related to the larger block chain system. These data structures may be hashed in multiple ways and comprise links to, or associations between nodes. These nodes can represent peers, projects, plans, protocol systems, databases or other block chains. Key aspects of this linked metadata will be stored graphically including descriptions of the relationship, or associated agreement between peers.
FUNCTIONAL DESCRIPTION
Part 6 of iPeerion mechanism that massively increases speed of transaction through precisely organized distribution across nodes (140,000 plus transactions per second).
Covers a variety of linked blockchain based data structures to store key information related to the larger block chain system. These data structures may be hashed in multiple ways and comprise links to, or associations between nodes. These nodes can represent peers, projects, plans, protocol systems, databases or other block chains. Key aspects of this linked metadata will be stored graphically including descriptions of the relationship, or associated agreement between peers.
ABSTRACT
The present invention is a network or tree-structured data structure for storing metadata related to a blockchain system. The data structure is also stored in a blockchain, and therefore inherits the properties of a blockchain- security in its recording. In an exemplary embodiment wherein the network or tree-like structure comprises key-value pairs, wherein, in some of the key value pairs, the key names a node or nodes that are hashed and the associated value is the hash of the node or nodes. In turn that key-value hash may also be included in a hash. The exemplary embodiment comprises links or associations between nodes, wherein nodes relate to to peers, projects, plans, systems, databases or other blockchains. In the case where nodes name peers in a network, the graphical associations may store elements that are named by the key or the key-value pair representing the association. The value may store the role of the node in a relationship or association; or the terms in an agreement, plan, or the commitment of the peer named by the node and so forth, or the public key of the peer named by the key and so forth.
The present invention is a network or tree-structured data structure for storing metadata related to a blockchain system. The data structure is also stored in a blockchain, and therefore inherits the properties of a blockchain- security in its recording. In an exemplary embodiment wherein the network or tree-like structure comprises key-value pairs, wherein, in some of the key value pairs, the key names a node or nodes that are hashed and the associated value is the hash of the node or nodes. In turn that key-value hash may also be included in a hash. The exemplary embodiment comprises links or associations between nodes, wherein nodes relate to to peers, projects, plans, systems, databases or other blockchains. In the case where nodes name peers in a network, the graphical associations may store elements that are named by the key or the key-value pair representing the association. The value may store the role of the node in a relationship or association; or the terms in an agreement, plan, or the commitment of the peer named by the node and so forth, or the public key of the peer named by the key and so forth.
11. A BLOCKCHAIN SYSTEM AND METHOD FOR CONVERTING A COMMODITY TO CURRENCY
FUNCTIONAL DESCRIPTION
Example 2 (of many); Specific use-case for iPeerion technology.
When integrated into a well-formed and customized digital framework (including both digital currency and a robust digital exchange platform) high-value commodities (such as gold, oil reserves or precious gems) access tremendous leverage of value, through mobility and liquidity. Future value commodities such as electric power and clean water have access to the same advantages while simultaneously allowing access to these commodities for a much larger pool of stakeholders. This patent covers the process of securely recording all aspects of these high value commodities on the blockchain, including origin, transport, processing, associated transactions and value.
FUNCTIONAL DESCRIPTION
Example 2 (of many); Specific use-case for iPeerion technology.
When integrated into a well-formed and customized digital framework (including both digital currency and a robust digital exchange platform) high-value commodities (such as gold, oil reserves or precious gems) access tremendous leverage of value, through mobility and liquidity. Future value commodities such as electric power and clean water have access to the same advantages while simultaneously allowing access to these commodities for a much larger pool of stakeholders. This patent covers the process of securely recording all aspects of these high value commodities on the blockchain, including origin, transport, processing, associated transactions and value.
ABSTRACT
In a computer network having a blockchain a messaging network for reporting and recording all phases of acquiring-producing, transporting, transforming and selling said commodity, said commodity having significant value such as gold or precious gems. The computer network is secured having cryptographic encoding of messages sent to the blockchain. Cryptographic encoding comprises and is not limited to encoding with a Vernam cipher. Devices transmitting cryptographic messages are pre-assigned and registered on a blockchain and the devices have digital fingerprints that are sent with each message. Operators of devices sending messages have access to said device by a biometric signature that is required to operate said device and is sent with every message. For each message sent, a hash is computed and sent with said message. In the exemplary embodiment, the hash comprises: 1. The message; 2. The digital signature of the device; 3. The biometric signature of the operator of the device; and 4. A code sent by the system controlling the blockchain. Each message is a blockchain record that is blockchained with the previously sent message blockchain record.
In use, devices sending messages comprise desktop computers, laptop computers, cellphones, iPads (or equivalent), drones and satellites. It is anticipated but not required that messages will be sent at the following phases:
In a computer network having a blockchain a messaging network for reporting and recording all phases of acquiring-producing, transporting, transforming and selling said commodity, said commodity having significant value such as gold or precious gems. The computer network is secured having cryptographic encoding of messages sent to the blockchain. Cryptographic encoding comprises and is not limited to encoding with a Vernam cipher. Devices transmitting cryptographic messages are pre-assigned and registered on a blockchain and the devices have digital fingerprints that are sent with each message. Operators of devices sending messages have access to said device by a biometric signature that is required to operate said device and is sent with every message. For each message sent, a hash is computed and sent with said message. In the exemplary embodiment, the hash comprises: 1. The message; 2. The digital signature of the device; 3. The biometric signature of the operator of the device; and 4. A code sent by the system controlling the blockchain. Each message is a blockchain record that is blockchained with the previously sent message blockchain record.
In use, devices sending messages comprise desktop computers, laptop computers, cellphones, iPads (or equivalent), drones and satellites. It is anticipated but not required that messages will be sent at the following phases:
- Seeding or initial location of the commodity;
- Growth or extraction phases;
- Transport;
- Conversion or processing;
- Sale.
12. SCADA SMART CONTRACT
FUNCTIONAL DESCRIPTION
Example 1 (of many); Specific use-case for iPeerion technology.
Covers an executable (library of) protocols, stored on blockchain, that monitor SCADA signals linked to the flow of an asset, which asset flow is under contract/agreement between a producer and consumer. Whenever the flow of the asset deviates from the agreement, protocol(s) can intervene in any of number of ways all of which may be predefined, with all above activities recorded on the blockchain.
FUNCTIONAL DESCRIPTION
Example 1 (of many); Specific use-case for iPeerion technology.
Covers an executable (library of) protocols, stored on blockchain, that monitor SCADA signals linked to the flow of an asset, which asset flow is under contract/agreement between a producer and consumer. Whenever the flow of the asset deviates from the agreement, protocol(s) can intervene in any of number of ways all of which may be predefined, with all above activities recorded on the blockchain.
ABSTRACT
Stored in a block-chain, a computer executable monitor for monitoring SCADA signals controlling the flow of an asset, wherein the monitored signals have levels that correspond to asset flow agreed by contract between a producer and a consumer of the asset. Deviations of said contract signals are stored in a block-chain. Deviations may also cause a computer executable function stored in the block-chain to be called. The blockchain stored computer executable function may call the producer, or the consumer or both. The computer executable function may also modify the control signal to change the rate of flow of the asset. Any changes made by the computer executable function is also recorded in the blockchain.
Stored in a block-chain, a computer executable monitor for monitoring SCADA signals controlling the flow of an asset, wherein the monitored signals have levels that correspond to asset flow agreed by contract between a producer and a consumer of the asset. Deviations of said contract signals are stored in a block-chain. Deviations may also cause a computer executable function stored in the block-chain to be called. The blockchain stored computer executable function may call the producer, or the consumer or both. The computer executable function may also modify the control signal to change the rate of flow of the asset. Any changes made by the computer executable function is also recorded in the blockchain.
13. BLOCKCHAINED NEXUS FOR THE INTERNET OF THINGS
FUNCTIONAL DESCRIPTION
Central element of iPeerion platform – blockchain management of IoT
A blockchain based method for indexing (unique identifiers), finding through search, instructing/controlling through protocols and recording the activities (on associated blockchain) of interlinked devices.
Note: IoT and VPP are intimately linked for iPeerion, being operated, recorded, transacted on the same hardware (home-node-server) iPeerion designed and iPeerion software driven, thus providing a high value private network of nodes for blockchain transacting.
FUNCTIONAL DESCRIPTION
Central element of iPeerion platform – blockchain management of IoT
A blockchain based method for indexing (unique identifiers), finding through search, instructing/controlling through protocols and recording the activities (on associated blockchain) of interlinked devices.
Note: IoT and VPP are intimately linked for iPeerion, being operated, recorded, transacted on the same hardware (home-node-server) iPeerion designed and iPeerion software driven, thus providing a high value private network of nodes for blockchain transacting.
ABSTRACT
The present invention is disclosed in three exemplary embodiments, each embodiment comprising:
The present invention is disclosed in three exemplary embodiments, each embodiment comprising:
- A mechanism, for associatively searching key-value pairs, wherein a key is used as a search argument, with a value, or no value returned, and;
- A data structure comprising the key-value pair stored in a blockchain that is searched by the associative mechanism
14. BLOCKCHAIN HYBRID CONTRACT
FUNCTIONAL DESCRIPTION
Part 2: Legal documents such as contracts designed for, executed and recorded on blockchain.
Covers any use of a contract on blockchain when combined with a method of execution also stored on the blockchain. The signal initiating the contract may come from a peer on the network or through the execution of another contract or series of contracts. May involve virtual machines to execute contracts regardless of operating system.
FUNCTIONAL DESCRIPTION
Part 2: Legal documents such as contracts designed for, executed and recorded on blockchain.
Covers any use of a contract on blockchain when combined with a method of execution also stored on the blockchain. The signal initiating the contract may come from a peer on the network or through the execution of another contract or series of contracts. May involve virtual machines to execute contracts regardless of operating system.
ABSTRACT
A hybrid contract stored in a blockchain. The hybrid contract, as a software container, is comprised of: a text section that records an agreement between two or more parties. Included, and associated with the text section, is at least one link (perhaps an API, or a remote procedure call- RPC) to one or more processes, or executable code, or to SQL for a database and so forth. The executable code may be embedded in the hybrid contract or may reside in a node or a software container in a distributed network. However, the executable code is stored in at least one blockchain. The link activated by an external signal or message. The external signal or message is sent by a peer of the contract parties or by another hybrid contract. The external signal or message is recorded in a blockchain. The software container may also include a virtual machine that facilitates execution of the hybrid contract on Microsoft, Apple and Linus systems.
A hybrid contract stored in a blockchain. The hybrid contract, as a software container, is comprised of: a text section that records an agreement between two or more parties. Included, and associated with the text section, is at least one link (perhaps an API, or a remote procedure call- RPC) to one or more processes, or executable code, or to SQL for a database and so forth. The executable code may be embedded in the hybrid contract or may reside in a node or a software container in a distributed network. However, the executable code is stored in at least one blockchain. The link activated by an external signal or message. The external signal or message is sent by a peer of the contract parties or by another hybrid contract. The external signal or message is recorded in a blockchain. The software container may also include a virtual machine that facilitates execution of the hybrid contract on Microsoft, Apple and Linus systems.
15. A PROXY FOR USER INTERACTION WITH A BLOCKCHAIN
FUNCTIONAL DESCRIPTION
Allows a program to take over for a person, precursor to AI directing personal affairs, all of which is stored/implemented on blockchain.
Covers any use of a “program” within blockchain that acts on behalf of a user and performs functions on behalf of the user. All of which is further recorded in blockchain.
FUNCTIONAL DESCRIPTION
Allows a program to take over for a person, precursor to AI directing personal affairs, all of which is stored/implemented on blockchain.
Covers any use of a “program” within blockchain that acts on behalf of a user and performs functions on behalf of the user. All of which is further recorded in blockchain.
ABSTRACT
A user proxy for interacting with a server having a blockchain database is disclosed; the user interacting through a client. The proxy comprises a first model and a second model; each model simulating objects, actions, associations and relationships. Objects simulated may be persons, machines, assets, products, services, producers and consumers. The second model includes actions, associations and relationships that simulate the interactions of objects and the results or benefits or detriments from interactions. Through the first model, a user selects a subset of the second model; the selected second model subset having a beginning state and at least one final state. Through the first model, the user directs the execution of the second model. The user proxy includes software to compute a hash of “snapshots” or transcripts of the second model, and to write a representation of the hashed snapshots to the server blockchain, and integrate the hash into a blockchain record, as currently practiced. The blockchain is either updated or not updated by the final state of the second model.
A user proxy for interacting with a server having a blockchain database is disclosed; the user interacting through a client. The proxy comprises a first model and a second model; each model simulating objects, actions, associations and relationships. Objects simulated may be persons, machines, assets, products, services, producers and consumers. The second model includes actions, associations and relationships that simulate the interactions of objects and the results or benefits or detriments from interactions. Through the first model, a user selects a subset of the second model; the selected second model subset having a beginning state and at least one final state. Through the first model, the user directs the execution of the second model. The user proxy includes software to compute a hash of “snapshots” or transcripts of the second model, and to write a representation of the hashed snapshots to the server blockchain, and integrate the hash into a blockchain record, as currently practiced. The blockchain is either updated or not updated by the final state of the second model.
16. ACTIVE LEGAL DOCUMENT IN A BLOCKCHAIN
FUNCTIONAL DESCRIPTION
Part 1: Legal documents such as contracts designed for, executed and recorded on blockchain.
Covers any use of a “APIs” or “links” or “processes” (protocols) within blockchain that “call up” legal text or instructions which will interact directly or indirectly with the development of new blockchain. Similar to the use of links in website text which redirect to, or open, a new page, wherein the text now includes the terms and conditions of the contract(s). The protocols can make decisions on whether those terms and conditions have been met. They can verify when that contract is complete, and now the protocol engine can move on to next processes in the protocol library which may be to call up a script program and/or API to take next actions. This could include consensus across nodes, etc.
FUNCTIONAL DESCRIPTION
Part 1: Legal documents such as contracts designed for, executed and recorded on blockchain.
Covers any use of a “APIs” or “links” or “processes” (protocols) within blockchain that “call up” legal text or instructions which will interact directly or indirectly with the development of new blockchain. Similar to the use of links in website text which redirect to, or open, a new page, wherein the text now includes the terms and conditions of the contract(s). The protocols can make decisions on whether those terms and conditions have been met. They can verify when that contract is complete, and now the protocol engine can move on to next processes in the protocol library which may be to call up a script program and/or API to take next actions. This could include consensus across nodes, etc.
ABSTRACT
A data structure for interacting indirectly with a data queue through a content addressing mechanism. The data structure comprises legal text linked to an API that calls an external process interacting indirectly with a data queue. Data in the queue is indirectly addressed by a content addressable memory that is stored in a blockchain. The blockchain may reside in the queue. The link to the API may be digitally signed and encrypted, and may be passed to the external process. The link may be externally activated by another process, or by clicking on the text.
A data structure for interacting indirectly with a data queue through a content addressing mechanism. The data structure comprises legal text linked to an API that calls an external process interacting indirectly with a data queue. Data in the queue is indirectly addressed by a content addressable memory that is stored in a blockchain. The blockchain may reside in the queue. The link to the API may be digitally signed and encrypted, and may be passed to the external process. The link may be externally activated by another process, or by clicking on the text.
17. DISTRIBUTED EXCHANGE FOR CRYPTOCURRENCIES
FUNCTIONAL DESCRIPTION
(a) Central element of iPeerion platform – A distributed digital exchange platform.
Token exchange requires blockchain protocols, and equally importantly requires a robust, efficient, trusted exchange and distributed is the future of exchange. Covers a digital exchange platform that employs blockchain based distribution OF the action of exchange of digital currencies across the network. Includes search of nodes (member/user accounts), and consolidation of nodes to fulfill transactions. Establishes a trusted distributed “bank”, with associated “digital-checks” which enable high-speed transactions without interface to traditional currency exchange services.
(b) Point-of-Sale and “Diaspora” funds made easy.
Expansion/application of above: A Physical unit in store that can accept a customer’s wallet number and passcode/ encryption key and immediately confirm transactions without the need to engage a bank is the near future application. Including:
1. A POS system that accepts crypto currencies, or a single designated one, utilizing blockchain for transacting.
2. This system is backed by above patented distributed exchange, “digi check” and fast transacting iPeerion (Orr) cluster tech.
3. Online purchase of the currency using credit cards can be offered, given a trusted source that can distribute and honor the exchange to physical currency can be situated in the country of implementation. This can be offered as a method of purchasing tokens for future use, or done for the exact amount for the purpose of a single transaction at POS.
4. This mechanism enables low-cost transfer, receipt and (local) use of “diaspora” funds worldwide.
FUNCTIONAL DESCRIPTION
(a) Central element of iPeerion platform – A distributed digital exchange platform.
Token exchange requires blockchain protocols, and equally importantly requires a robust, efficient, trusted exchange and distributed is the future of exchange. Covers a digital exchange platform that employs blockchain based distribution OF the action of exchange of digital currencies across the network. Includes search of nodes (member/user accounts), and consolidation of nodes to fulfill transactions. Establishes a trusted distributed “bank”, with associated “digital-checks” which enable high-speed transactions without interface to traditional currency exchange services.
(b) Point-of-Sale and “Diaspora” funds made easy.
Expansion/application of above: A Physical unit in store that can accept a customer’s wallet number and passcode/ encryption key and immediately confirm transactions without the need to engage a bank is the near future application. Including:
1. A POS system that accepts crypto currencies, or a single designated one, utilizing blockchain for transacting.
2. This system is backed by above patented distributed exchange, “digi check” and fast transacting iPeerion (Orr) cluster tech.
3. Online purchase of the currency using credit cards can be offered, given a trusted source that can distribute and honor the exchange to physical currency can be situated in the country of implementation. This can be offered as a method of purchasing tokens for future use, or done for the exact amount for the purpose of a single transaction at POS.
4. This mechanism enables low-cost transfer, receipt and (local) use of “diaspora” funds worldwide.
ABSTRACT
The distributed exchange of digital currencies relies on a network created by distributing the action OF exchange. Each member of the network connects their digital currency wallet, and method of payment (credit card information, PayPal account information, or distributed digital token and/or “Digi Check” account/wallet) to the application. When an individual want to “purchase” digital currency, he or she request from the network the amount to purchase. The network will search through all the nodes on the network for what are on offer. If the requested total of crypto currency cannot be fulfilled by a single offeror/seller, a number of sellers’ offerings will be consolidated to make up the value of crypto currency required. On the click of “purchase”, the crypto currency on offer, from one or more sources, will be transferred to the purchaser’s wallet. At the same time, the compensation of will be split and transferred to the sellers’ accounts. The purchaser received the full crypto currency requested, and the culmination of offerings will be compensated in kind. As an extension, a trusted source can offer “Digi Checks”, which is a crypto currency like token which carries the same value as the fiat currency payed for it. Not unlike regular checks, these “Digi Checks” can be exchanged for currency, and vice versa by the trusted source at any time. This enables speedy transacting without having to interface into any traditional currency exchange services.
The distributed exchange of digital currencies relies on a network created by distributing the action OF exchange. Each member of the network connects their digital currency wallet, and method of payment (credit card information, PayPal account information, or distributed digital token and/or “Digi Check” account/wallet) to the application. When an individual want to “purchase” digital currency, he or she request from the network the amount to purchase. The network will search through all the nodes on the network for what are on offer. If the requested total of crypto currency cannot be fulfilled by a single offeror/seller, a number of sellers’ offerings will be consolidated to make up the value of crypto currency required. On the click of “purchase”, the crypto currency on offer, from one or more sources, will be transferred to the purchaser’s wallet. At the same time, the compensation of will be split and transferred to the sellers’ accounts. The purchaser received the full crypto currency requested, and the culmination of offerings will be compensated in kind. As an extension, a trusted source can offer “Digi Checks”, which is a crypto currency like token which carries the same value as the fiat currency payed for it. Not unlike regular checks, these “Digi Checks” can be exchanged for currency, and vice versa by the trusted source at any time. This enables speedy transacting without having to interface into any traditional currency exchange services.
18. VIRTUAL POWER-PLANT ENABLED BY A PROXY STORED IN A BLOCKCHAIN
FUNCTIONAL DESCRIPTION
Example 3 (of many); Specific use-case for iPeerion technology.
Covers the blockchain based control of a system/network/microgrid of electrical devices (control systems, storage, production, use, etc.) to organize benefits to each participant (homeowner, business, utility, grid etc.) either in management of power, or in terms of value/revenue generated. This includes directing where power goes and when, and recording all transactions involving electrons.
Note: iPeerion protocols (utility and device software interfaces) for enabling/connecting all components within (and external to such virtual power plants also includes the nodes (control servers) and software to manage system physically and record on blockchain.
FUNCTIONAL DESCRIPTION
Example 3 (of many); Specific use-case for iPeerion technology.
Covers the blockchain based control of a system/network/microgrid of electrical devices (control systems, storage, production, use, etc.) to organize benefits to each participant (homeowner, business, utility, grid etc.) either in management of power, or in terms of value/revenue generated. This includes directing where power goes and when, and recording all transactions involving electrons.
Note: iPeerion protocols (utility and device software interfaces) for enabling/connecting all components within (and external to such virtual power plants also includes the nodes (control servers) and software to manage system physically and record on blockchain.
ABSTRACT
A system and method for a virtual power plant comprising a protocol residing in a blockchain that stores and controls the selection of plans for producing, allocating, distributing and storing electrical power. The protocol, using logic such as rule-based or neural-net AI accepts inputs that are requests for the disposition of electrical power. Logic in the protocol elects plans that conform to requests, and existing contracts, and conntrols SCADA that allocates and distributes power from sources to sinks. Decisions made by the protocol are stored in a blockchain, and by algorithms, select or modify plans to optimize the economic benefit of participating peers.
A system and method for a virtual power plant comprising a protocol residing in a blockchain that stores and controls the selection of plans for producing, allocating, distributing and storing electrical power. The protocol, using logic such as rule-based or neural-net AI accepts inputs that are requests for the disposition of electrical power. Logic in the protocol elects plans that conform to requests, and existing contracts, and conntrols SCADA that allocates and distributes power from sources to sinks. Decisions made by the protocol are stored in a blockchain, and by algorithms, select or modify plans to optimize the economic benefit of participating peers.
19. BLOCKCHAIN NEXUS- A COMPUTER MECHANISM ENABLING DISTRIBUTED GOVERNANCE AND CONSENSUS IN A BLOCKCHAIN NETWORK
FUNCTIONAL DESCRIPTION
A distributed high speed blockchain based processing platform - integration of iPeerion subsystems.
This patent covers incremental growth of blockchain based processing capacity, storage and speed through the coordination and distribution of tasks and functions across a network of peers, and includes protocol libraries (behavior templates), with proprietary mechanisms for security, indexing, referencing, search, authentication, consensus, while recording/storing all states (transactions, path, method and outcomes) in the associated blockchain.
FUNCTIONAL DESCRIPTION
A distributed high speed blockchain based processing platform - integration of iPeerion subsystems.
This patent covers incremental growth of blockchain based processing capacity, storage and speed through the coordination and distribution of tasks and functions across a network of peers, and includes protocol libraries (behavior templates), with proprietary mechanisms for security, indexing, referencing, search, authentication, consensus, while recording/storing all states (transactions, path, method and outcomes) in the associated blockchain.
ABSTRACT
In a computer network of peers interacting with a blockchain, a nexus for peer interaction, the nexus comprising a protocol encoding peer behaviors according to a contract or agreement, the protocol also encoding peer consensus and governance for said transaction or project; a peer interface to said protocol, whereby peers interact through virtual references provided by the protocol, and; an associative mechanism for translating virtual references to physical references.
In a computer network of peers interacting with a blockchain, a nexus for peer interaction, the nexus comprising a protocol encoding peer behaviors according to a contract or agreement, the protocol also encoding peer consensus and governance for said transaction or project; a peer interface to said protocol, whereby peers interact through virtual references provided by the protocol, and; an associative mechanism for translating virtual references to physical references.
20. VIRTUAL SYSTEM FOR BLOCKCHAINS (EXPANDS ON 19 ABOVE)
FUNCTIONAL DESCRIPTION
A distributed high speed blockchain based processing platform - integration of iPeerion subsystems.
This patent covers incremental growth of blockchain based processing capacity, storage and speed through the coordination and distribution of tasks and functions across a network of peers, and includes protocol libraries (behavior templates), with proprietary mechanisms for security, indexing, referencing, search, authentication, consensus, while recording/storing all states (transactions, path, method and outcomes) in the associated blockchain.
FUNCTIONAL DESCRIPTION
A distributed high speed blockchain based processing platform - integration of iPeerion subsystems.
This patent covers incremental growth of blockchain based processing capacity, storage and speed through the coordination and distribution of tasks and functions across a network of peers, and includes protocol libraries (behavior templates), with proprietary mechanisms for security, indexing, referencing, search, authentication, consensus, while recording/storing all states (transactions, path, method and outcomes) in the associated blockchain.
ABSTRACT
An invention to enable the exchange of signals among processing elements in a distributed network having a blockchain, said signals enabled by virtual means. A first component of the invention assigns virtual references to processing elements and a second component of the invention translates virtual references to physical references and connects processing elements by physical reference.
An invention to enable the exchange of signals among processing elements in a distributed network having a blockchain, said signals enabled by virtual means. A first component of the invention assigns virtual references to processing elements and a second component of the invention translates virtual references to physical references and connects processing elements by physical reference.
21. NEURAL NETWORK FOR CRYPTOCURRENCY VALUATION
FUNCTIONAL DESCRIPTION
Intelligent adjudication system for cryptocurrency valuation
Currently, there are a couple of trading platforms that buffer crypto currency/token prices and somewhat protect against pump-and-dump “abuses” of this emerging market. The strategies used are relatively limited, and certainly not comprehensive in addressing many of the weaknesses inherent in a multi-(random) token environment. New strength and much sought-after stability can be added to the crypto marketplace, especially as the number of tokens increase, by the introduction of an intelligent algorithm-based adjudication system that can rank cryptocurrencies based on real world characteristics such as value, stability, trade pattern, reputation ranking, asset backing, revenue backing, technology backing, supply, demand, and other independent factors that together paint a more comprehensive picture of the value propositions and rating indices within the context of the entire marketplace, which will provide a tremendous boost of confidence, market intelligence, stability, enhanced liquidity, fair-value adjudication, and trading efficiency for the owner/investors and companies alike.
FUNCTIONAL DESCRIPTION
Intelligent adjudication system for cryptocurrency valuation
Currently, there are a couple of trading platforms that buffer crypto currency/token prices and somewhat protect against pump-and-dump “abuses” of this emerging market. The strategies used are relatively limited, and certainly not comprehensive in addressing many of the weaknesses inherent in a multi-(random) token environment. New strength and much sought-after stability can be added to the crypto marketplace, especially as the number of tokens increase, by the introduction of an intelligent algorithm-based adjudication system that can rank cryptocurrencies based on real world characteristics such as value, stability, trade pattern, reputation ranking, asset backing, revenue backing, technology backing, supply, demand, and other independent factors that together paint a more comprehensive picture of the value propositions and rating indices within the context of the entire marketplace, which will provide a tremendous boost of confidence, market intelligence, stability, enhanced liquidity, fair-value adjudication, and trading efficiency for the owner/investors and companies alike.
ABSTRACT
Herein is disclosed a system and method for learning and predicting the values and relative values of cryptocurrencies. Relative values are converted to correlation coefficients and stored in a blockchain for later prediction. In a first embodiment, in a system of cryptocurrencies, each cryptocurrency having a value, a neural network for learning and predicting relationships among values of said cryptocurrencies, and for further predicting the relationships in terms of commodity values. In a second embodiment, in a system of cryptocurrencies, each cryptocurrency having a value, a neural network for learning and predicting relationships among values of said cryptocurrencies, and for further predicting the relationships in terms of commodity values. In a third embodiment, in a system of cryptocurrencies, each cryptocurrency having a value, a neural network for learning and predicting relationships among values of said cryptocurrencies, and for further predicting the relationships in terms of social network sentiments. In a fourth embodiment, in a system of cryptocurrencies, each cryptocurrency having a value, a first neural network for learning and predicting relationships among values of said cryptocurrencies, and a second neural network for predicting cryptocurrency values in terms of inputs selected from the set comprising (social sentiments, commodity values, stock values).
Herein is disclosed a system and method for learning and predicting the values and relative values of cryptocurrencies. Relative values are converted to correlation coefficients and stored in a blockchain for later prediction. In a first embodiment, in a system of cryptocurrencies, each cryptocurrency having a value, a neural network for learning and predicting relationships among values of said cryptocurrencies, and for further predicting the relationships in terms of commodity values. In a second embodiment, in a system of cryptocurrencies, each cryptocurrency having a value, a neural network for learning and predicting relationships among values of said cryptocurrencies, and for further predicting the relationships in terms of commodity values. In a third embodiment, in a system of cryptocurrencies, each cryptocurrency having a value, a neural network for learning and predicting relationships among values of said cryptocurrencies, and for further predicting the relationships in terms of social network sentiments. In a fourth embodiment, in a system of cryptocurrencies, each cryptocurrency having a value, a first neural network for learning and predicting relationships among values of said cryptocurrencies, and a second neural network for predicting cryptocurrency values in terms of inputs selected from the set comprising (social sentiments, commodity values, stock values).